React App Security Best Practices
React security flaws may not be evident to the naked eye, but they might be fatal to your web application. JavaScript has a long record of being linked to widespread security flaws. Reactjs is identical. Components of several javascript libraries include security issues that have led to thousands of installs, some of which can be fatal to sensitive data of your React web application and thus it becomes important to learn about react app security.
With the help of our India based React developers, we have designed this blog post that will demonstrate how to swiftly address React App Security Flaws and decrease the chance of security issues accumulating in your web app over time.
1. The Most Common React.js Cyberattacks
As per Snyk, each time React.js is updated, undetected security vulnerabilities are introduced. Consequently, it is hard to account for all potential assaults to which React.js (or other frameworks) may be susceptible. Nevertheless, below are the most prevalent ones. Let’s investigate them in further depth.
1.1 Cross-Site Scripting (XSS)
XSS is a significant client-side issue. An attacker is able to insert malicious code into your application or software that is perceived as genuine and performed as a component of the React app. This undermines the app’s functioning and user data.
Two forms of cross-site scripting attacks exist:
- Reflected XSS — In this scenario, a hacker utilizes a malicious link containing JS script that the computer interprets to obtain and modify the web pages, cookies, and other vital user-provided data.
- Stored XSS — In this approach, a malicious script is saved on a server and then performed when a user accesses the stored data. This results in undesirable data breaches on your website.
1.2 Distributed Denial of Service (DDoS)
DDoS threats overload the architecture of a web application with more data than it can manage. Their goal is to prevent consumers from accessing a program. UDP, ICMP, SYN, and HTTP query flooding are among the most used DDoS attack techniques. Since servers and application firewalls must process and reply to every query of a react application, the hacker attempts to deplete storage and unit’s processing time.
1.3 SQL Injection
SQL Injection attacks, also known as SQLi, is a common web application attacks. The cybercriminal intends to get confidential material that should not be exposed by manipulating confidential data. In order to collect contact information, credit card info, and other data, attackers seek to acquire critical information.
This response-react cybersecurity technique allows hackers to manage server access, extract data, and alter database settings.
1.4 XML External Entity Attack (XXE)
An XXE attack occurs when the perpetrator attacks the XML parser necessary to convert XML into usable code.
They inject harmful code into parsers to capture confidential data or even execute CSRF and DDoS attacks.
1.5 Cross-Site Request Forgery (CSRF)
A perpetrator commits a CSRF attack by crafting a message or web page that convinces a victim to execute a state-changing demand on the web application. It may include transferring payments or issuing authorization, among other things. Typically, a hacker uses links or invisible graphics to execute GET, POST, or PUT requests via a form. These requests may also be constructed with malicious JavaScript code, but users’ browsers will block it unless the server-side session manager specifically permits it.
1.6 Zip Slip
The malicious person attacks this issue by uploading zip files that contain harmful or unauthorized react code. React developers allow the addition of zip files to reduce file sizes when uploading. When the application decompresses the archive, the infected file(s) can corrupt other files or execute code. Attackers can either damage the host system’s data or obtain unauthorized access to the machine.
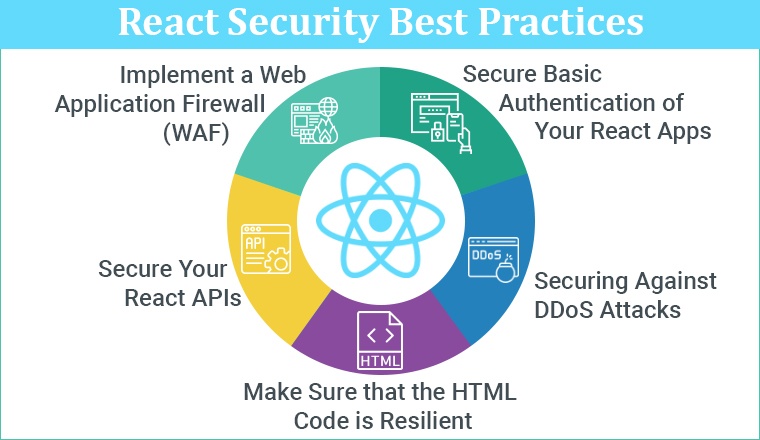
2. React Security Best Practices
As the saying goes, an abundance of caution is better than a cure; thus, it is often a smart option to adhere to established standards and maintain the security of your application.
You may not consider every potential weakness but you can keep your web application safer by reducing the most prevalent security threats.
Below are some of the recommended methods for securing your React applications:
2.1 Secure Basic Authentication of Your React Apps
Ensure that the communication between the host and the user is encrypted. This is a fundamental but crucial security vulnerability of your application.
Verify that your app’s domain heading has a realm property as a straightforward method for achieving this goal. A realm keeps a database of authorized visitors and demands login details to read protected content.
This section describes how to establish a security realm:
<security-realm name="App-Realm"> <authentication> <local default-user="$local" allowed-users="comma-separated-list"/> <properties path="application-users.properties"/> </authentication> <authorization> <properties path="application-roles.properties"/> </authorization> </security-realm> |
When feasible, multi-factor authentication is a simple and reliable method of authentication. This approach makes sure that a visitor is only provided access to critical sections of your app after giving login information for identity verification.
Per each new registration, you must always generate a fresh session ID using a highly secured session manager.
If your React.js application has basic strong access in place, XSS and broken authentication concerns are mitigated.
2.2 Securing Against DDoS Attacks
Generally, these sorts of security vulnerabilities occur when the software has weaknesses in masking the IPs of servers or when the web application is insufficiently secure.
Solution: You may limit the number of visits from a given origin to a particular IP using API rate limitations.
2.3 Make Sure that the HTML Code is Resilient
Any React program will require HTML code for rendering, hence it is essential that your HTML page is secure. Three effective approaches to accomplish this are:
A. Disable HTML markups
Whenever an HTML item’s ‘disabled’ property is set, the react component becomes immutable. This element cannot be selected or submitted via a form.
Then, you may add validation and only activate the element if you meet the criteria. This avoids the submission of malicious data that might have catastrophic consequences.
Below is an instance of code for disabling a button:
const App = () => { const [submitting, setSubmitting] = useState(false); const handleSubmit = () => { setSubmitting(true); ....... // Code for the actions setSubmitting(false); } return( <div> <button type="button" disabled={} onClick={handleSubmit}>Submit</button> </div> ); } ReactDOM.render( <App />, document.getElementById('app-container')); |
B. Use escape characters
JavaScript XML (JSX) is a format that enables HTML coding in React apps. And you may utilize its built-in auto-escaping ability to safeguard your application.
By standard, if you link data using curly brackets, React will release numbers that are not included in the linked data.
Here’s one specific example:
return (<span style={{backgroundColor: bgColor}}>{myAppRating}</span>); |
If a hacker attempts to introduce additional code like shades: purple, background-color: pinkish into the field myAppColor, the JSX parser will identify this improper CSS input. Therefore, the extra information will flee, and the assault will be rendered ineffective.
C. Utilize dangerously
Your program may have to display dynamic HTML code such as data supplied by the user. This is accomplished through innerHTML, which renders the application susceptible to malicious code.
The dangerouslySetInnerHTML attribute is a functionality of React that can alert you to this particular risk. This serves as a caution so you can verify that the information input while this property is present originates from a reliable source.
return (<p dangerouslySetInnerHTML={{__html: myHtmlDescription}}></p>); |
You can also use libraries like DOMPurify to scan user input and remove malicious content.
import DOMPurify from 'dompurify'; var clean = DOMPurify.sanitize(dirty); |
// Sanitize the review
return (<p dangerouslySetInnerHTML={{__html: myHtmlDescription}}></p>); |
Suppose that a hacker adds the following ‘onerror’ code to the object:
const myHtmlDescription = (<><b>Bold</b>and<i>Italic.</i> <img src=”mypicture.png” onerror=”alert(‘This app is infected with virus!’);” /></>);
All of these safeguards your React app from XSS and arbitrary code execution security threats.
2.4 Secure Your React APIs
The advantages and disadvantages of React APIs are that they enable connections across your application and external services. They are able to store information and execute commands. This exposes your application to XSS and SQL injection vulnerabilities.
Verifying all API functions relative to respective API schemas is a strong mitigating strategy against this security issue. In addition, plan regular schema test cases and encrypt all transactions with SSL/TLS.
Use innocuous characters rather than delivering data over APIs for increased security.
2.5 Implement a Web Application Firewall (WAF)
A WAF is a software filter that monitors, analyzes, and filters incoming traffic in order to discover and prevent harmful material.
There are three techniques to establish a web application firewall:
- Hardware-level network-based firewall protection.
- The integrated host-based firewall within the program.
- Cloud-based WAF
WAF’s signature-based filtration is highly efficient against SQL injection, XSS, execution of unauthorized code, and zip slip. Implementing a Web Application Firewall is one of the finest React security best practices.
3. Common React js App Security Checklist
- Disable all markup-containing instructions
- With Jscrambler, keep react js secure.
- Implementing idle timeout is crucial.
- Utilize snippet technologies, like ES7 React, Redux, and others.
- Perform Reactjs code reviews, using whitelists to restrict all app inputs.
- Utilize detection software, a web application firewall, and serialized javascript NPM packages to strengthen app security.
- Analyze your code for react app security vulnerabilities and possibly dangerous code, like URLs and HTML elements.
- Employ Adequate authentication methods.
- Examine the dataset for SQL injection flaws and validates every API function against the API Schema.
4. Conclusion
When developing a React application, you must consider a variety of possible security risks. Without adequate protection, your application may become the target of hackers, which can result in monetary loss, time wastage, trust violations, and legal difficulties.
With security hazards emerging daily and attackers abusing more and more vulnerabilities, securing your React application may be fairly complicated and challenging.
You may either recruit security-focused React developers or outsource the production to a software development firm that specializes in the creation of React JS applications. Make certain you have a professional like us on your side when it is the security and privacy we are talking about!

Hardik Dhanani has a strong technical proficiency and domain expertise which comes by managing multiple development projects of clients from different demographics. Hardik helps clients gain added-advantage over compliance and technological trends. He is one of the core members of the technical analysis team.
Among all the other tech stacks, JavaScript is one of the few globally accepted scripting languages, and there are several JavaScript frameworks to select from....
 Aug 5, 2022
Aug 5, 2022 



Indeed, it is excellent content and a valuable blog. Thank you for putting together this list of the best React app security best practices! Your contribution to the ReactJS developers' community will surely be helpful. Keep up the great work. Thank you for sharing this!
Security is the most essential thing to consider while developing any web application. ReactJS is a robust Javascript library, it provides various inbuilt security options but you did a good job by providing the list of React app security best practices. From now on will check all the security threats before deploying an app. Thanks!